Find Out Who’s Tracking You Through Your Phone
codes for smartphones all in one video, together with some instructions on how to detect intruders. The status of the different types of diversions that are taking place along with the number the information is being transferred to will be displayed on your phone’s screen if you dial *#21#. It’s a good idea to dial ##002# you have to use roaming. In this case, money won’t be taken from your account for calls that are redirected by default to your voice mail. People usually don’t reveal all that much in phone conversations. From the point of view of those who want to listen in, it’s much more worthwhile to set up special devices ("bugs") in someone’s home. Radio wave detectors can be used to work out whether such bugs are present in a building. Determine what information it’s safe to make accessible to all. Be very careful when posting photographs of children. Only your mobile operator should ever offer you tracking services, and they should only turn them on with your explicit agreement. Websites and applications that offer to find out the location of other people are almost certainly acting with criminal intent.
TIMESTAMPS
*#21# 0:35
*#62# 1:21
*#06# 2:03 The James Bond Code 2:39
Use Anti-Virus Software 4:28
How do the secret services listen in? 5:05
How can you protect yourself from criminals and spies? 6:06
#phonehackers #phonetracking #protectphone
SUMMARY
-With *#21#, you can find out whether your calls, messages and other data are being diverted. -Dial *#62# if you want to find out where calls, messages, and data are being redirected to if it seems that no one can get through to you. -##002# is a universal code for switching off all forms of redirection away from your phone. -Dial *#06# to find out your IMEI (International Mobile Equipment Identifier). If you know this number, you can find your phone if someone steals it. -Special codes exist that allow someone to track your location and also to determine whether someone is following you. The ones to be suspicious of are mobile base stations — this could be a truck or small bus with a large antenna. -If you use Android, you should periodically check your phone for viruses. PlaceRaider is one of the most dangerous ones that can infect your device. -If a phone makes odd noises during a conversation, loses battery power rapidly, overheats, or unexpectedly restarts, this is merely an indication that you need to get it repaired rather than a telltale sign that you’re being listened to. -Use messaging apps that are completely closed to outsiders, such as Telegram, Chare, Wickr, or Signal. Don’t install unknown programs on your phone, keep close track of the apps you have installed, and use multiple security locks wherever you can.
Subscribe to Bright Side : https://goo.gl/rQTJZz
Alex Jones presents new scientific studies posted on the Drudge Report that completely confirm what he and Infowars have been reporting on for years: 5G can cause cancer and brain tumors.
TOTAL CONFIRMATION: 5G Linked To Cancer By More Scientific Studies
BREAKING: DARPA Admits 5G Designed To Slowly Kill Population
Smart Phones and Privacy Invasion
many of you know your small piece of technology that you carry around on a 24/7 daily grind is keeping tabs on you, whenever you like it or not. Modern day smart phones are tracking your every move whenever that be going for a casual scroll with your dog at your local park or having an evening shower in a hotel out of town. They not only constantly track your every move but they collect metadata such as browser history, fingerprints, voice commands, and facial recognition with the phones onboard camera and mic.
What we should know, what we do online is watched over, collected, exploited and sold, big brother is definitely watching you. Governments are collecting our information and storing it while selling it for numerous reasons such as consumerism, marketing, and profiling.
Data is collected to help better understand us but why is the government spying on us you would ask, well it comes down to control and profiling. Spying or the less invasive word monitoring governments would say they're protecting us but in reality they're not.
Even if you're not doing anything wrong, you're being watched and recorded. This is wrong and we the people should be entitled to privacy in our own home.
Below is listing of some of these phones abilities and the capacity of information they collect:
Facial and voice recognition
The constant Facial recognition for passwords is on the rise with extreme popularity in the recent years. Many apps have teamed up with this software and governments around the world have been implementing this form of ID in everyday life. You may see this process happenining in your airports, or simple grocery stores.
The FBI has been known for hacking into phones for a very long time. One of the programs they would use is called Gumfish, it allows access to hack both front and rear phones and the onboard mic on the cell phone.
Constant location monitoring
Even putting your cell phone into airplane or offline mode with turning off all wifi connections and networks, the phone will continue to collect information on you regardless if you have a sim card inserted or not. The cellphone will not only collect information offline it will store it then send it off to Google once it connects to the internet.
Internet browsers / applications
We have discussed that behind the scenes your cell phone is collecting data and sending it off but not only that your 3rd party applications and internet browsers whenever that be a cell phone, computer, or iPod, they all fall into the same category. Example, even if you opt out of the privacy settings on Google, it still tracks you without your consent.
Finger print scanning
A fingerprint scanner is a type of electronic security system that uses fingerprints for biometric authentication to grant a user access to information or to approve transactions. It used to be that fingerprint scanners were mostly seen in movies and TV shows, or read about in science fiction novels. Today we use this technology on our smart phones and can only predict that it is being stored, collected, and sold.
Want to know more regarding this article, check out the following videos
10 Surprising Ways the Government is Spying on You - YouTube
How to be anonymous on the web? Tor, Dark net, Whonix, Tails, Linux
The link below is a bunch of 3rd party apps that the general public can access in order to hack and spy into people's phones just a clear example if we can do it, they're already been doing it for much longer.
Top 10 Apps That Watch You - YouTube
Coveners League has many articles, here is a small sample, please check them out.
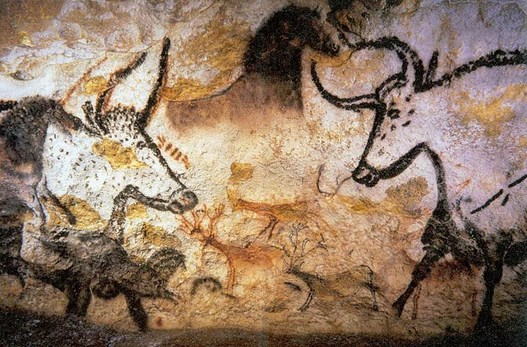
Teach White Europeans About Their Ice Age Heritage

White European Racial Pride. What Race Are You ?


White History, Music, Wars, Dances and Film Archives

Whites Fight Back Against Racism & Bigotry

European Birth Rate Statistics. Update 2
The Coudenhove-Kalergi plan - To Genocide Indigenous Europeans in Europe

US Constitution & Bill of Rights. Article…

Europe & Middle Eastern Wildlife. Update 2

Barbary Muslim Pirates Kidnapped Whites

Freedom of the Internet
The Thirty Years' War- Between Christians In

Genocide Whites & all Races

White Indigenous Rights

Promoting Large Families

Lauren Southern on South Africa: FARMLANDS (Are Whites History?)
Lauren Southern on South Africa: FARMLANDS (Are Whites History?)


The European Holocaust

Media Ownership: The Illusion of Choice
Fighting Genocide Worldwide


White Gentile Organizations & Jewish Community Based Organizations

White & Jewish National Congresses

Citizens Initizens Referendums ( CIR ) in Switzerland
Afrikaner AfriForum Civil Rights Organization
Orania White Afrikaner Community

Helping Whites. South African Family Relief …
I try to use copyright free images at all times. However if I have used any of your artwork or maps then please don't hesitate to contact me and I’ll be more than happy to give the appropriate credit.
27/10/2017p